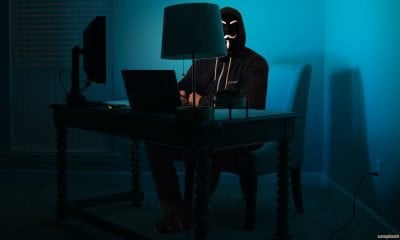
Millions of hack attempts are pitted against government organizations every day. Your business may not be as big a target as a national institution. You’re kidding...
Choosing a new career when you’ve been working for twenty or more years is a scary prospect for many people. However, there is one profession in...


Human error may be the single, most significant vulnerability in any security system. Therefore recognizing this threat is vital to implementing adequate security of any description,...
The fear businesses and people alike still have today is: will my documents arrive safely? Cybercriminals could and do intercept documents before they reach their intended...
According to CloudFare, cyberattacks are up by over a third, so there’s no time for your business to be complacent about online security and protecting your...



Who would have guessed 2020 would be about remote working and lockdowns. First, it was the supermarkets who changed their practices for the pandemic and then...
eCommerce businesses need to keep their online assets and their customer’s data safe from a host of threats. From spyware and malware to the corruption of...



When you have a business, one thing you should prioritize to is keeping it as safe as possible. You cannot take a risk with the security...



How secure is your data when working from home? It might be a lot better now; however, during the enforced lockdown, many workers telecommuting did so...



Seven out of ten customers say they would stop working with a company after it experiences a data breach. Hackers are not only targeting the IT...